Single Sign-on is a useful feature to increase security and user adoption of new tools. It means that your employees can auto-login to connected applications using their default company password, which is for instance stored in your LDAP or Active Directory system. While Small Improvements doesn’t integrate with LDAP or AD directly, it does integrate with a middleware called OneLogin.
OneLogin is a web-based middleware that connects the cloud applications you use with your internal Active Directory or LDAP servers. OneLogin has tons of features, but we’ll only need one, which is the SAML based SSO option. If you don’t have an OneLogin account yet, then you can use OneLogin entirely for free. Only if you want to connect more services later on you may want to pick a paid OneLogin plan.
Once configured, your staff can either access Small Improvements from the OneLogin dashboard or, if they access Small Improvements via your subdomain (e.g. https://mycompany.small-improvements.com) then OneLogin will ask them for the password – and after they key in their regular LDAP or AD password, we’ll let them on. No more multiple passwords!
Important: The OneLogin integration is only for SSO. We do not automatically synchronize your user accounts between systems yet. This is planned for the future, but right now you will have to keep your Small Improvements user accounts in sync with your directory service.
If a user doesn’t have an account in Small Improvements, then they won’t be able to log in. You can create user accounts manually, or send us an Excel spreadsheet.
How to set it up in less than 5 minutes
First, sign up for OneLogin and configure the connection to your LDAP or AD server. This will take a bit more time of course. But connecting Small Improvements and OneLogin is a walk in the park. You need to configure both systems. Here’s what needs to be done:
In OneLogin: Activate the Small Improvements app
Search the app directory and add Small Improvements to your portal:
Next, type in your Small Improvements subdomain. If you’re using https://mycompany.small-improvements.com, then type in “mycompany” here.
On the SSO tab of the application, you will need to locate the Issuer URL and the HTTP Endpoint URLs. Copy them to your clipboard so you have them in a minute.
Then, navigate to OneLogin’s “security” tab, and locate the “SAML” sub-tab. There, you’ll need the X.509 certificate text. Again, copy it somewhere so you can paste it into SI in a minute
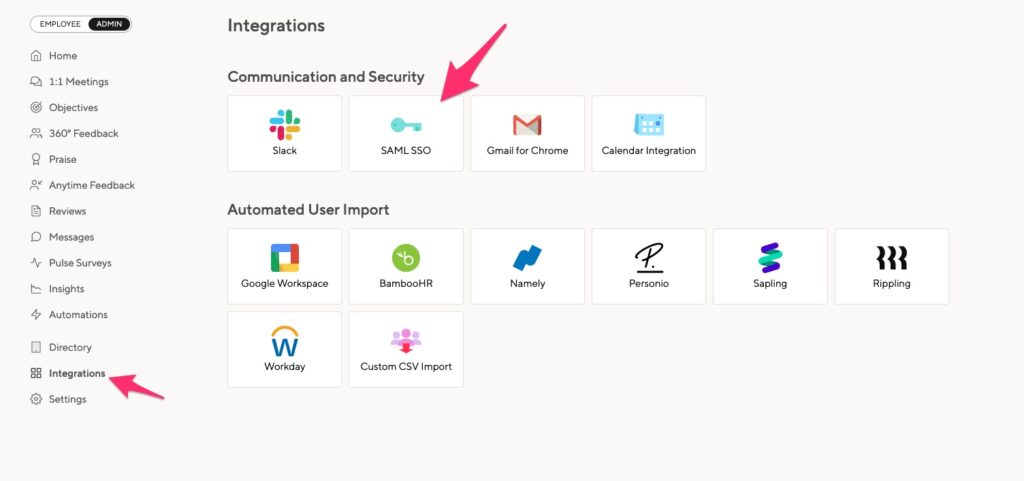
Now, go to the Small Improvements administration overview, and locate the SAML settings button:
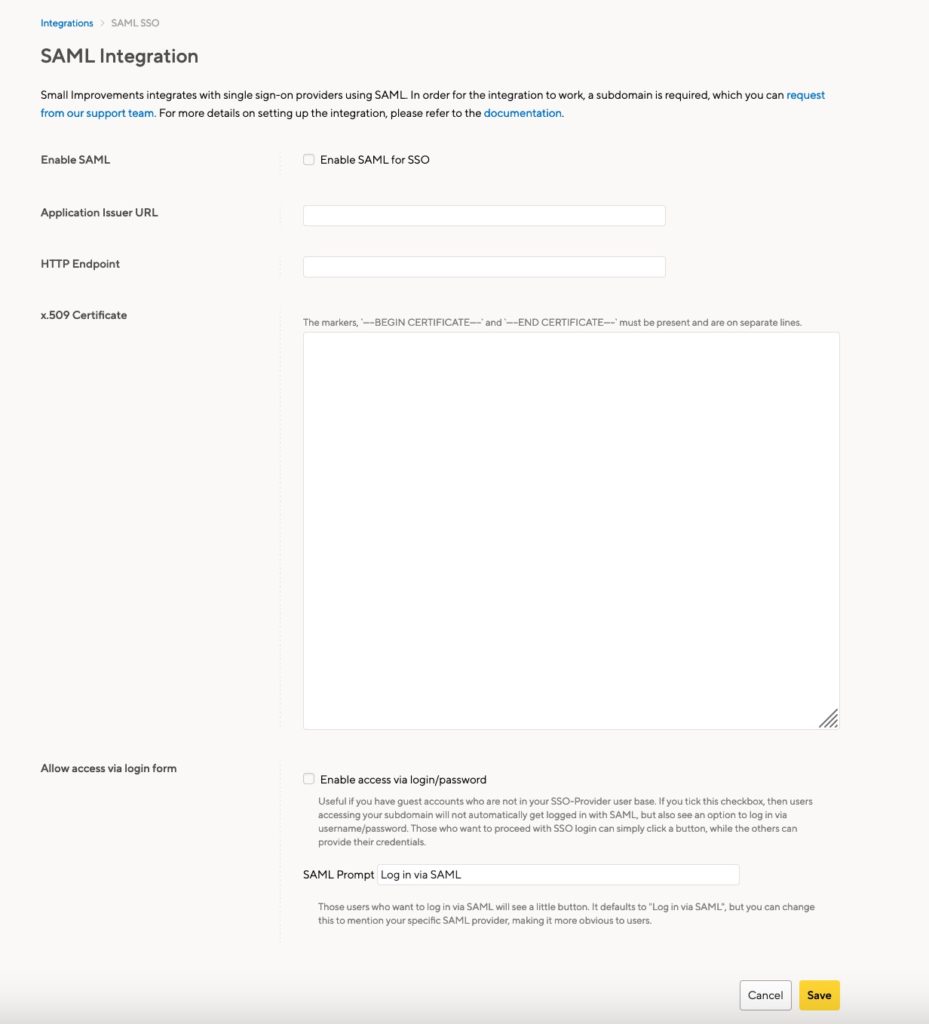
And on the actual config screen, enter in the X.509 certificate and the Issuer and Endpoint URLs you just obtained from OneLogin. Activate the integration, save the settings, and you’re done.
Add user-accounts
Now add user-accounts to Small Improvements via “Administration > User Directory” or import them from an Excel worksheet. Note: A user needs to be created in Small Improvements before he/she can log in.
Adjusting the welcome email
Important: You must adjust some emails to avoid confusion.
Whenever you invite staff into Small Improvements, they receive an email telling them about Small Improvements. This email also explains how to define their new password. But since they will use OneLogin’s password instead, that email template needs to get changed!.
Please locate the “Access to Small Improvements: Welcome Mail” email template, and remove any mention passwords setting. You can write that people should use the password defined in your intranet instead.
That’s it!
For this to work you will need a Small Improvements subdomain. Just let us know and we’ll have it up and running within 48 hours or so. Also, you will, of course, need to set up an account with OneLogin. That’s easy though, and the basic plan of OneLogin is free. Get started here.
Remember: OneLogin integration via SAML is only for SSO, it doesn’t help with user management. All users need to have an account on both systems already.
Troubleshooting
In case something doesn’t work with login via OneLogin (for instance because a user exists in SI but not in LDAP, or OneLogin doesn’t pull it from LDAP), and you still want that person to be able to log in, please manually define a password for them: Go to the user profile page, locate “admin” in the dropdown, and change their password. Tell the person their new password, and direct them to log in via the main SI website: https://www.small-improvements.com. Don’t use your company-specific subdomain, since that will typically redirect to OneLogin instantly. The www option will allow the user to log in manually.




